Using AWS Systems Manager in Hybrid Cloud Environments
Introduction
Hybrid and multicloud strategies are now the norm for enterprises seeking agility, resilience, and compliance. Yet, managing infrastructure that spans AWS, on-premises data centres, and even other public clouds introduces operational complexity and security challenges. AWS Systems Manager (SSM) provides a unified, scalable solution for automating, monitoring, and securing workloads across these diverse environments.

Why AWS Systems Manager for Hybrid Environments?
AWS SSM enables organisations to treat on-premises servers and VMs, whether Windows or Linux, just like EC2 instances. By registering these machines as “managed nodes”, you can apply consistent patching, configuration, and compliance policies across your entire estate. This approach eliminates silos, reduces manual effort, and enhances security posture.
Key benefits include:
Centralised management: One console for AWS, on-premises, and multicloud resources.
Consistent automation: Use the same SSM documents, maintenance windows, and automation scripts everywhere.
Unified compliance: Generate fleet-wide patch and compliance reports, regardless of location.
Secure operations: All actions are logged in AWS CloudTrail, and access is governed by IAM.

Architecture Overview
A robust hybrid SSM deployment typically includes:
SSM Agent: Installed on all managed nodes (EC2, on-premises, or other cloud VMs).
Private Connectivity: On-premises servers connect to AWS via Direct Connect or VPN, with VPC endpoints for SSM, S3, and related services to ensure no traffic traverses the public internet.
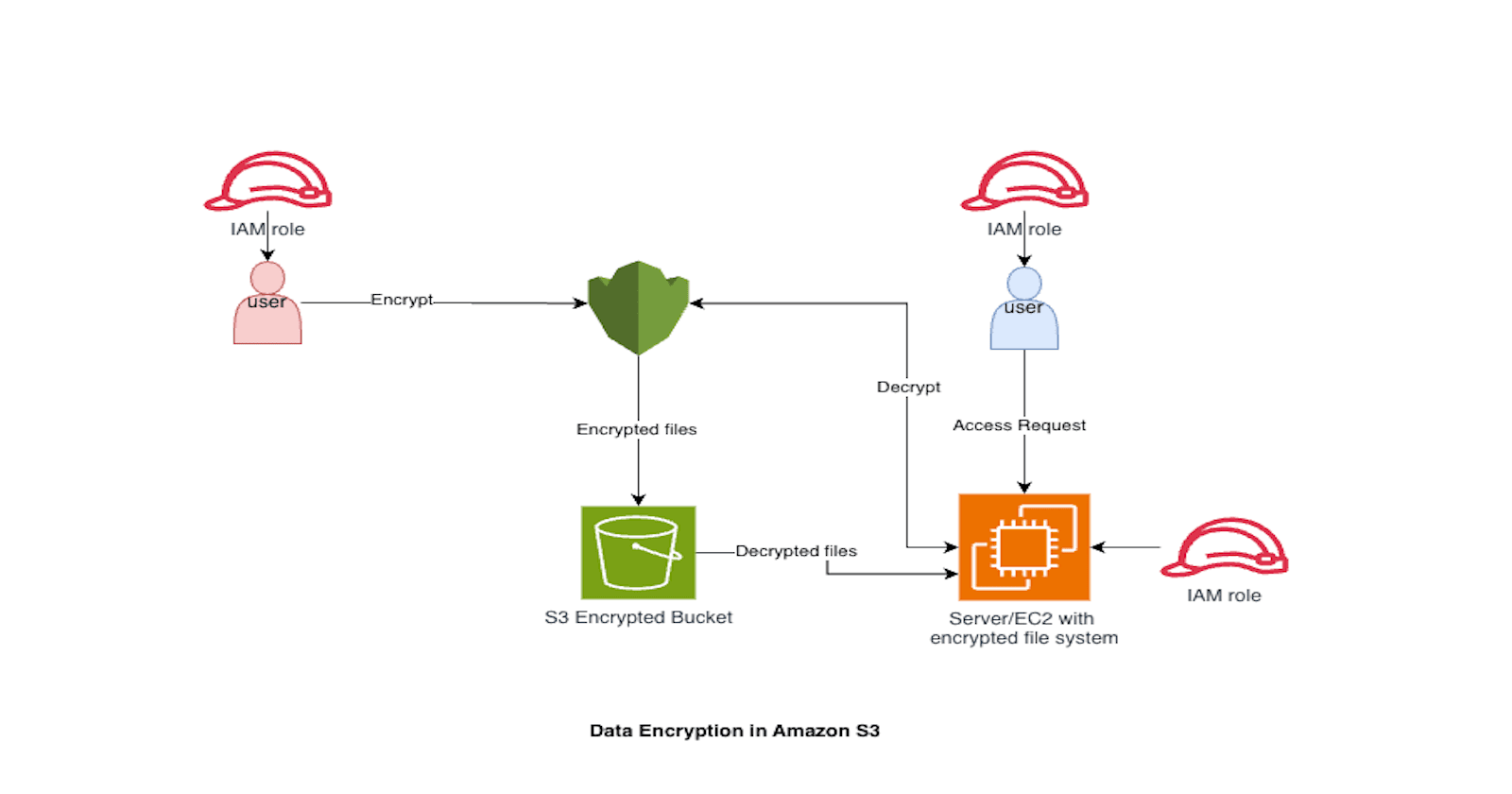
IAM Roles: Fine-grained roles for hybrid activations, with least-privilege permissions.
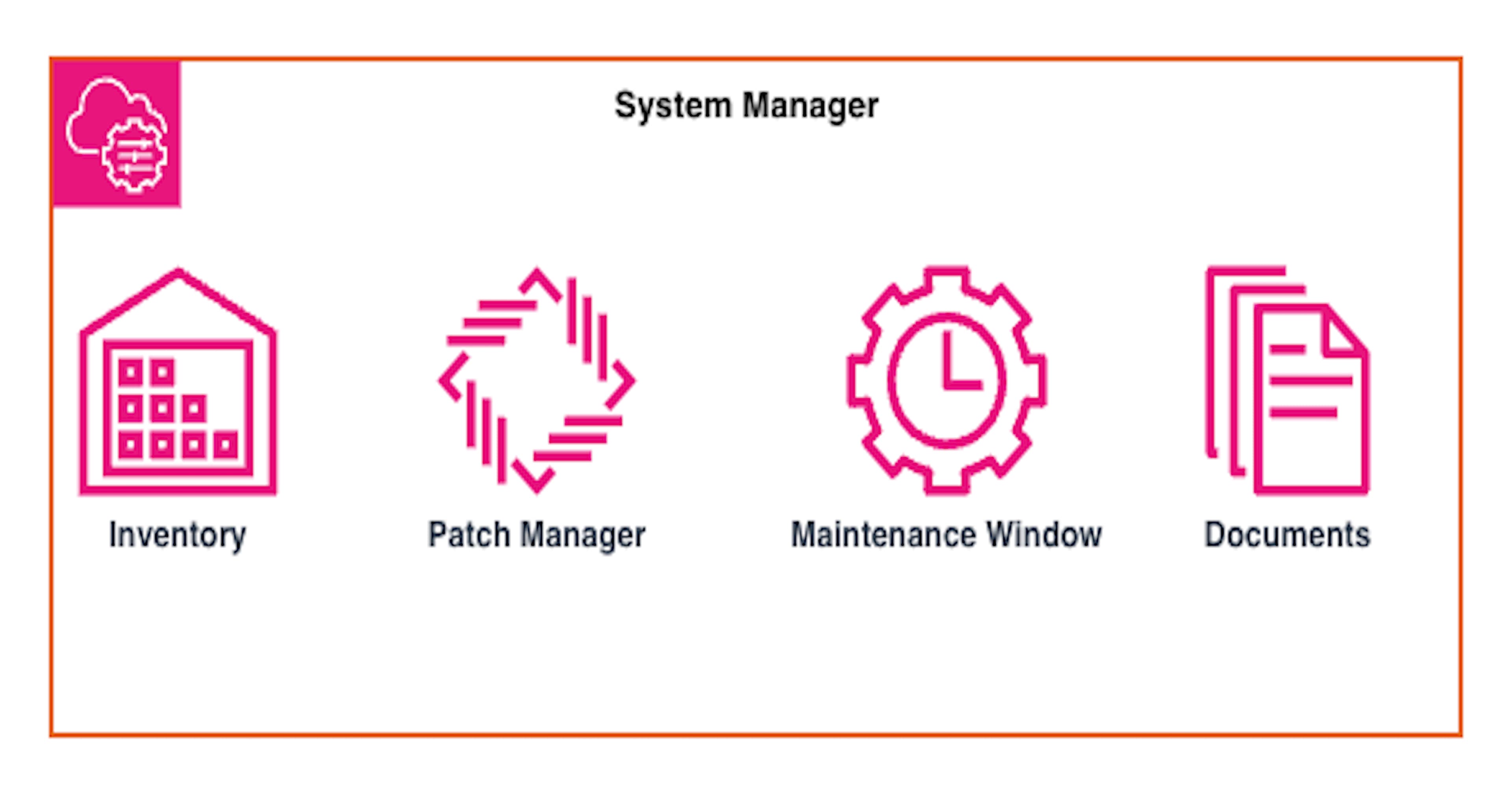
Patch Manager: Automates patch scanning, deployment, and compliance reporting.
CloudWatch & CloudTrail: For monitoring, alerting, and auditing.

Deep Dive: Network Architecture, VPC Endpoints, and Patch Source Requirements
Ensuring Secure, Private Connectivity with VPC Endpoints
In a well-architected hybrid SSM deployment, all communication between on-premises servers and AWS Systems Manager services must traverse private VPC endpoints—never the public internet. This is essential for both security and compliance, especially in regulated industries.
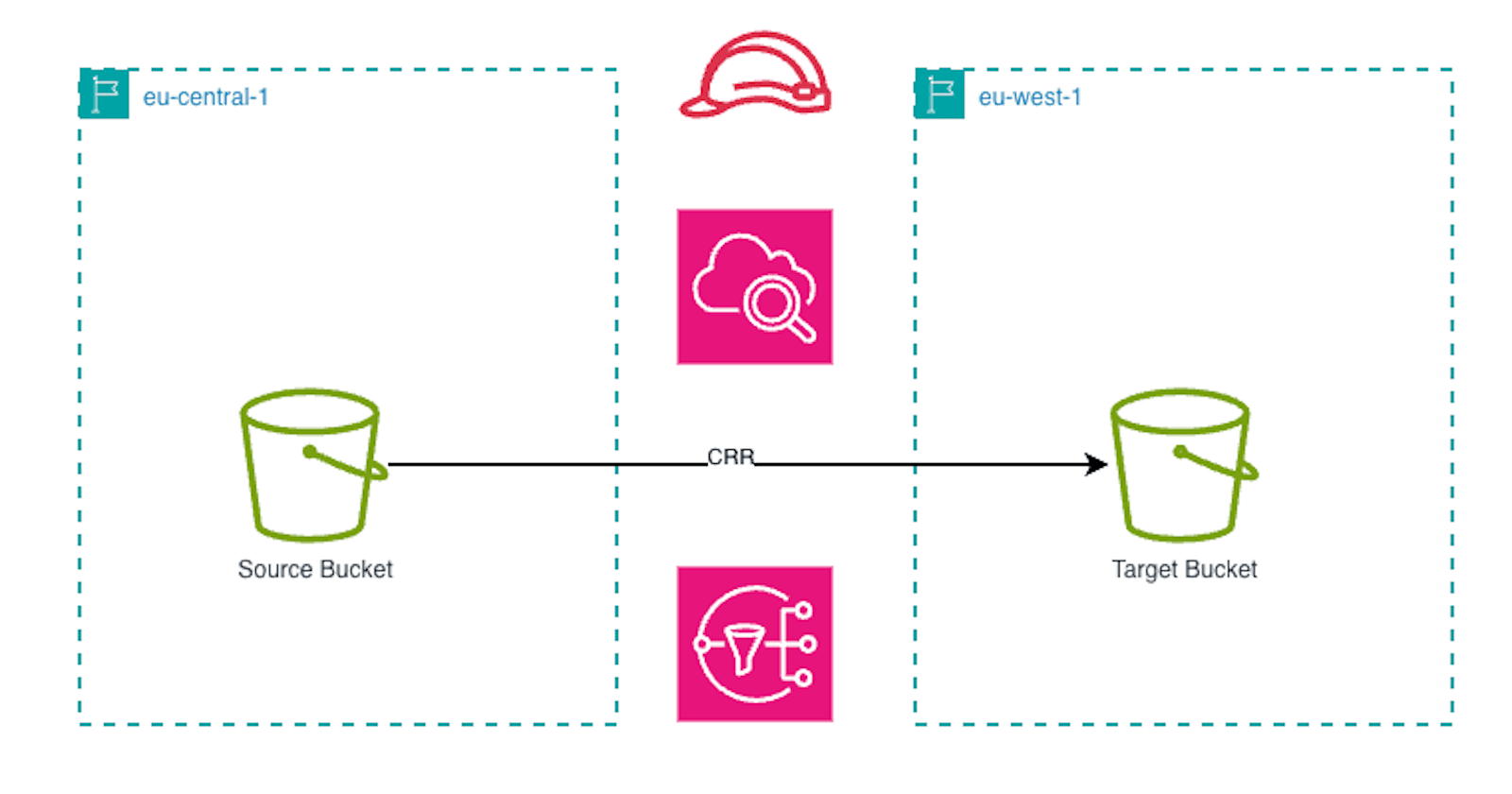
Centralising Endpoints in the Network Account
Within an AWS Organisation, it is best practice to centralise all VPC endpoints in a dedicated network account. This approach simplifies management, auditing, and ensures consistent security controls across all environments (Dev, Test, Prod). All on-premises and cloud-based managed nodes should route their SSM, S3, and related traffic through these endpoints.
VPC Endpoint Policies: Restricting Access to Patch Repositories
To enforce that all patching traffic flows exclusively through VPC endpoints, you must apply strict endpoint policies. Below is an example S3 VPC endpoint policy that only allows access to the patch repository bucket from the endpoint itself:
SSM and Related Endpoint Policies
For SSM, SSM Messages, and EC2 Messages endpoints, use endpoint policies that restrict access to only the required AWS services and resources. Example:
{
"Statement": [
{
"Effect": "Allow",
"Principal": "",
"Action": "ssm:SendCommand",
"Resource": ""
}
]
}
Best practice:
Limit actions and resources as tightly as possible.
Regularly review endpoint policies for least-privilege access.
Patch Source Requirements: WSUS and Satellite Servers
While AWS Patch Manager orchestrates patching, the actual patch binaries for on-premises servers must still be sourced from local repositories:
Windows Servers:\ Require connectivity to a local WSUS (Windows Server Update Services) server. This ensures that Windows updates are distributed efficiently and in compliance with internal policies.\ Note: Direct internet access to Microsoft Update is not recommended for enterprise environments.
Linux Servers (e.g., Red Hat):\ Must have access to a Red Hat Satellite server or equivalent local repository. This is critical for environments with restricted internet access and for maintaining control over which updates are approved and deployed.
Why Local Patch Sources Are Mandatory
Bandwidth Efficiency: Downloading patches once to a local repository and distributing internally reduces WAN usage and speeds up patch deployment.
Compliance and Control: Organisations can vet and approve patches before they are made available to production systems.
Security: Prevents unmanaged or unapproved updates from being installed, and avoids exposing servers to the public internet
Advanced Setup: Hybrid Activation and Agent Configuration
1. Hybrid Activation
Hybrid activation is the process of registering non-EC2 machines (on-premises or other clouds) as managed nodes in SSM. This involves:
Creating an activation in the SSM console, specifying the instance limit, IAM role, and expiry.
Installing the SSM Agent on each server and registering it using the activation code and ID.
For large estates, automate agent deployment and registration using configuration management tools (e.g., Ansible, Chef, or PowerShell DSC).
2. Agent Configuration for Secure Connectivity
Update the amazon-ssm-agent.json file on each managed node to:
Point to VPC endpoints for SSM, S3, and EC2 messages.
Disable public internet access.
Configure logging and telemetry to CloudWatch or S3 for centralised monitoring.
Example configuration snippet:
{
"Ssm": { "Endpoint": "ssm.region.amazonaws.com" },
"Mds": { "Endpoint": "ec2messages.region.amazonaws.com" },
"Mgs": { "Endpoint": "ssmmessages.region.amazonaws.com" },
"S3": { "Endpoint": "PATCH-LOG-BUCKET.s3-region.amazonaws.com" }
}
3. IAM and Security
Patch Manager, a feature of SSM, automates patching for both operating systems and supported applications (limited to Microsoft updates on Windows). It supports:
Patch Baselines: Define which patches are approved, auto-approve rules, and exceptions.
Patch Groups: Use tags to group servers for targeted patching.
Maintenance Windows: Schedule patching to minimise business impact.
Compliance Reporting: Generate detailed reports on patch status and compliance.
4. Advanced Patch Orchestration
Integrate Patch Manager with automation pipelines (e.g., Jenkins, GitHub Actions) for CI/CD-driven patching.
Use custom SSM documents to handle complex patching scenarios, such as pre- and post-patch validation, or application-aware patching.
For multicloud, ensure SSM Agent is supported and network connectivity is secured for each cloud provider.
Monitoring, Auditing, and Compliance
CloudWatch: Collect metrics and logs from all managed nodes, set up alarms for patch failures or compliance drift.
CloudTrail: Audit all SSM actions, including who initiated patching or configuration changes.
Athena & QuickSight: Query and visualise compliance data at scale for audits and executive reporting.
Best Practices and Lessons Learned
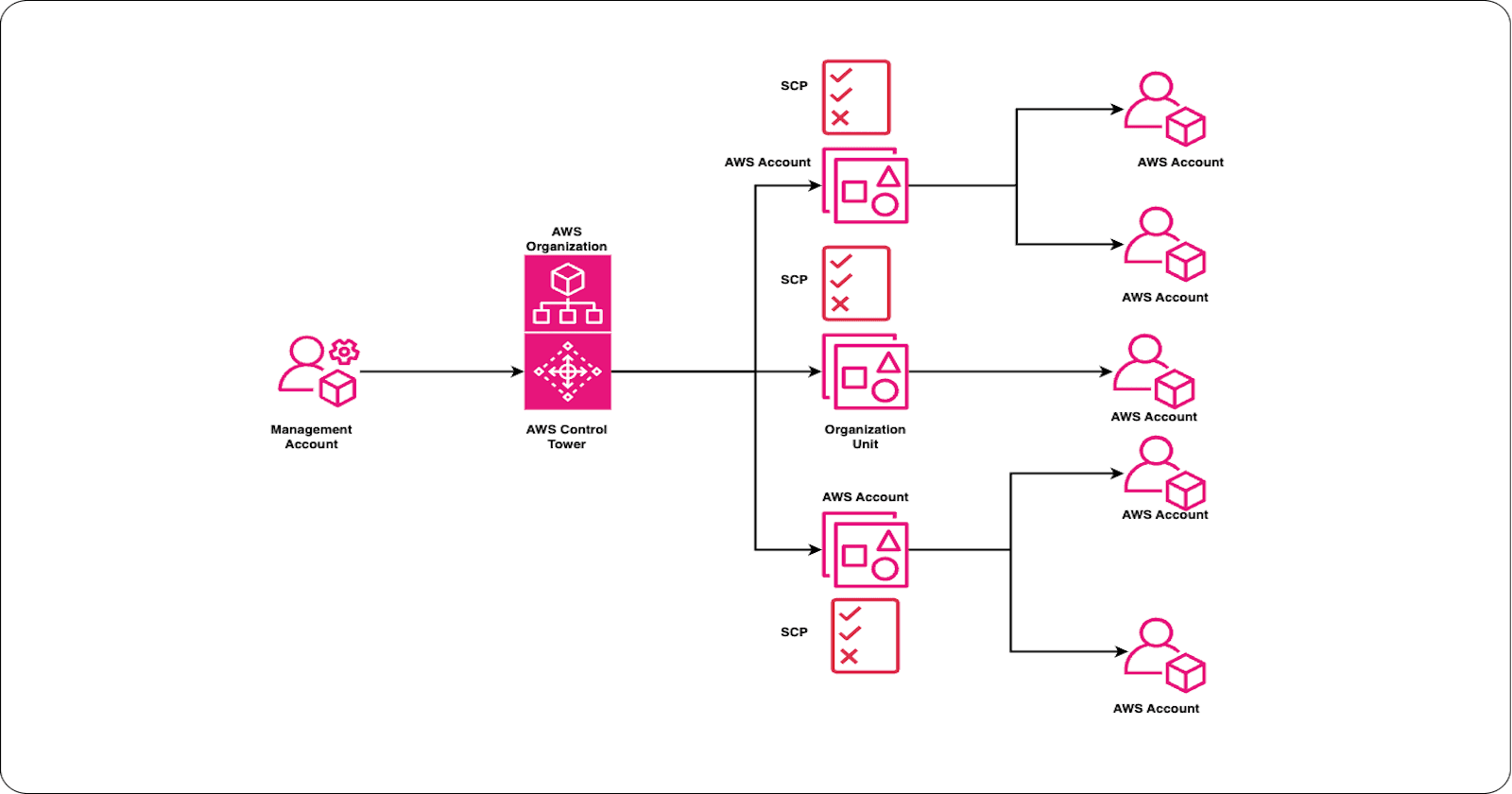
Segregate environments: Use separate activations and IAM roles for Dev, Test, and Prod.
Automate everything: From agent deployment to compliance reporting, leverage automation to reduce manual errors.
Test patching in lower environments before rolling out to production.
Monitor agent health: Regularly check that all managed nodes are online and reporting.
Document and review: Maintain clear documentation of your hybrid SSM setup, and periodically review IAM policies and network configurations.
End-to-End Patch Flow in a Hybrid Environment
Patch Manager schedules a scan or deployment via SSM.
SSM Agent on each managed node receives instructions via the VPC endpoint.
On-premises Windows servers fetch updates from WSUS; Linux servers fetch from Satellite.
Patch status and compliance data are sent back to AWS via the VPC endpoint.
All logs and compliance reports are centralised in S3, accessible only via the endpoint.
Security and Audit Considerations
All patching and SSM traffic must be logged and auditable via CloudTrail and VPC Flow Logs.
No direct internet access should be permitted from managed nodes for patching.
IAM roles and endpoint policies must be reviewed regularly to ensure least-privilege.
Conclusion
AWS Systems Manager, when properly architected, delivers enterprise-grade automation, compliance, and security across hybrid and multicloud estates. By enforcing strict VPC endpoint policies, mandating WSUS and Satellite servers for on-premises patch sources, and following advanced setup practices, such as private connectivity, robust IAM, and automated patch orchestration, organisations can achieve operational excellence and regulatory compliance, while reducing risk and manual effort.