Automating AWS Governance with Account Factory for Terraform (AFT)
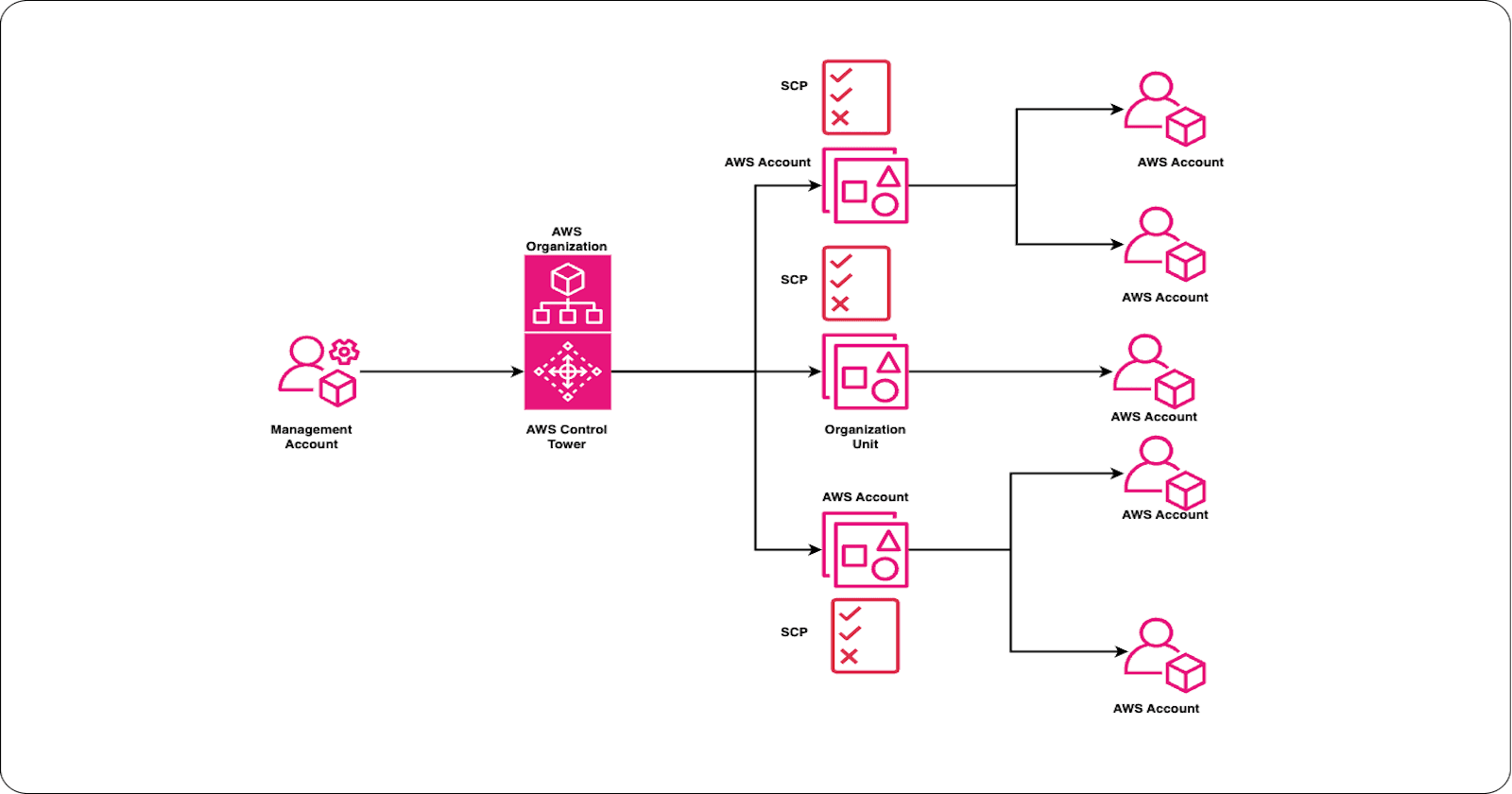
As organizations scale their cloud footprint, managing AWS accounts with consistent governance, security, and customization becomes increasingly complex. AWS Control Tower Account Factory for Terraform (AFT) bridges this gap by combining the governance of AWS Control Tower with the flexibility of Terraform. This blog explores AFT’s architecture, deployment models, customization capabilities, and operational features that make it a cornerstone for cloud platform teams.
Overview of AFT
AFT is a Terraform-based orchestration framework that automates the provisioning and customization of AWS accounts in a Control Tower landing zone. It enables platform teams to adopt a GitOps-style workflow, where account lifecycle operations are managed through version-controlled repositories.
Key Benefits:
Terraform-native provisioning with support for Terraform Cloud, Enterprise, and OSS.
Governance integration with AWS Control Tower.
Customizations applied globally or per-account.
Git-based workflows via AWS CodeCommit or external VCS providers.
Architecture
AFT operates in a dedicated AFT management account, separate from the Control Tower management account. The architecture includes:
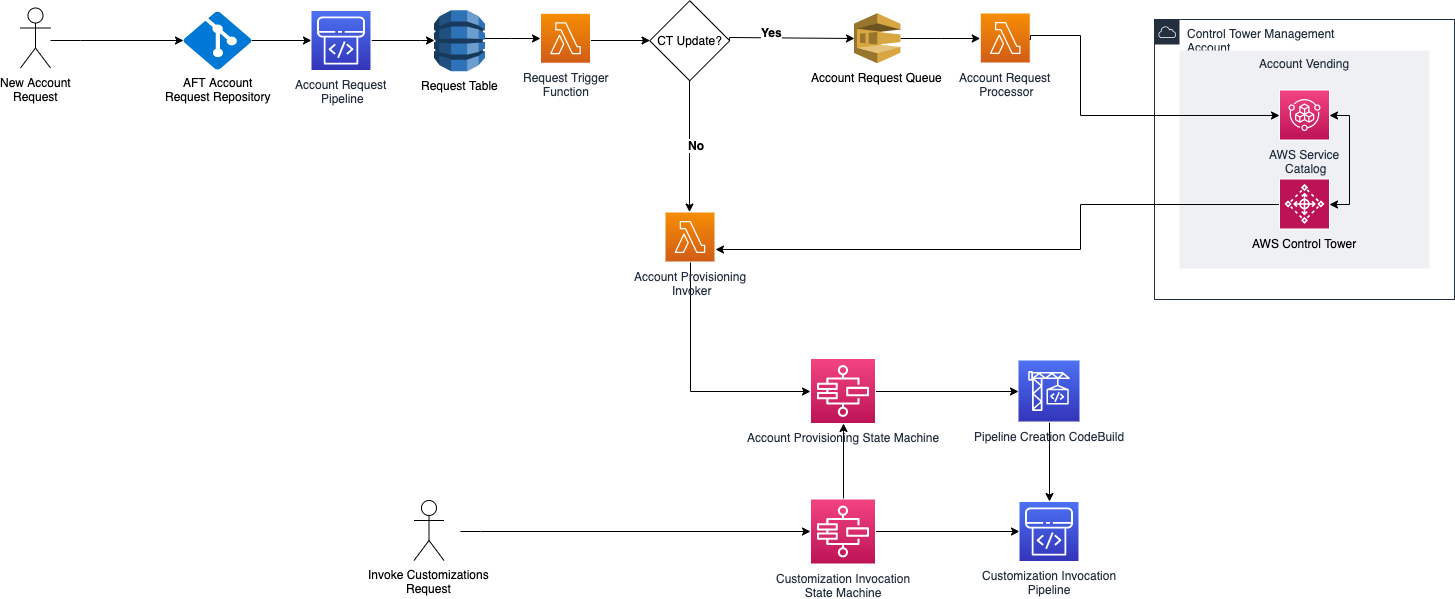
Account Request Pipeline: Users submit Terraform files to a Git repo.
Provisioning Engine: AFT provisions accounts via Control Tower.
Global Customizations: Common configurations applied to all accounts.
Account-Specific Customizations: Tailored settings based on metadata.
Audit and Traceability: CloudWatch Logs and unique tokens for tracking.
This modular design ensures scalability, traceability, and compliance across large AWS environments.
Deployment Models
AFT supports both single-account and multi-account provisioning:
Single Account: Ideal for testing or small teams.
Multiple Accounts: Supports concurrent provisioning for enterprise-scale environments.
Prerequisites:
AWS Control Tower landing zone.
AFT management account.
Terraform runtime environment.
Git repository (CodeCommit or external).
Optional configurations: VPC, encryption, tagging, compute resources.
Required Roles and Permissions
AFT requires specific IAM roles to operate securely:
AFT Management Role: Deployed in the AFT management account to orchestrate pipelines.
Account Customization Role: Assumes permissions in target accounts for applying configurations.
Terraform Execution Role: Manages Terraform operations securely.
Cross-Account Access Roles: Enable customization and logging across accounts.
These roles should follow least privilege principles and be monitored via AWS CloudTrail.
Customizations and Data Protection
AFT supports global and account-specific customizations using Terraform modules. Examples include:
Security Baselines: GuardDuty, IAM policies, SCPs.
Networking: VPC setup, Transit Gateway attachments.
Monitoring: CloudWatch alarms, dashboards.
Data Protection:
KMS Encryption: Encrypt logs, SNS topics, and other resources.
CloudTrail Integration: Organization-wide logging of data events.
Default VPC Removal: Enforce custom networking standards.
Customizations are version-controlled and auditable, ensuring compliance with data protection regulations.
Operational Metrics and Monitoring
AFT provides visibility into operations via:
CloudWatch Logs: Track provisioning and customization events.
Step Functions: Visualize workflow execution.
Custom Metrics:
Account provisioning success/failure rates.
Customization execution times.
Drift detection and reconciliation.
These metrics help platform teams optimize performance and troubleshoot issues proactively.
Updating and Removing Accounts
Updating Existing Accounts
AFT supports post-provisioning updates via manual customization requests. This allows teams to:
Apply new policies.
Update networking.
Modify tagging strategies.
All updates are logged and traceable.
Removing Accounts
While AFT does not directly delete accounts, it supports:
Decommissioning workflows: Custom Terraform modules to clean up resources.
Tagging for retirement: Mark accounts for manual review and deletion.
Audit Trails: Ensure all removal actions are logged.
Account removal should follow organizational policies and AWS best practices.
Feature Options
AFT offers several optional features to enhance governance and cost optimization :
CloudTrail Logging: Enable organization-level logging of data events.
Default VPC Deletion: Remove default VPCs to enforce custom networking standards.
Enterprise Support Enrollment: Automatically enroll accounts into AWS Enterprise Support.
KMS Encryption: Apply customer-managed keys to CloudWatch logs and SNS topics.
Custom Tags: Add metadata for cost allocation and resource tracking.
These features can be toggled via Terraform variables during deployment or updated later.
Conclusion
AWS Control Tower Account Factory for Terraform empowers platform teams to manage AWS accounts at scale with automation, governance, and flexibility. From provisioning to customization, monitoring, and decommissioning, AFT provides a robust framework that integrates seamlessly with modern DevOps workflows.
Ref: https://docs.aws.amazon.com/controltower/latest/userguide/aft-architecture.html