Data Encryption with Amazon S3
Introduction
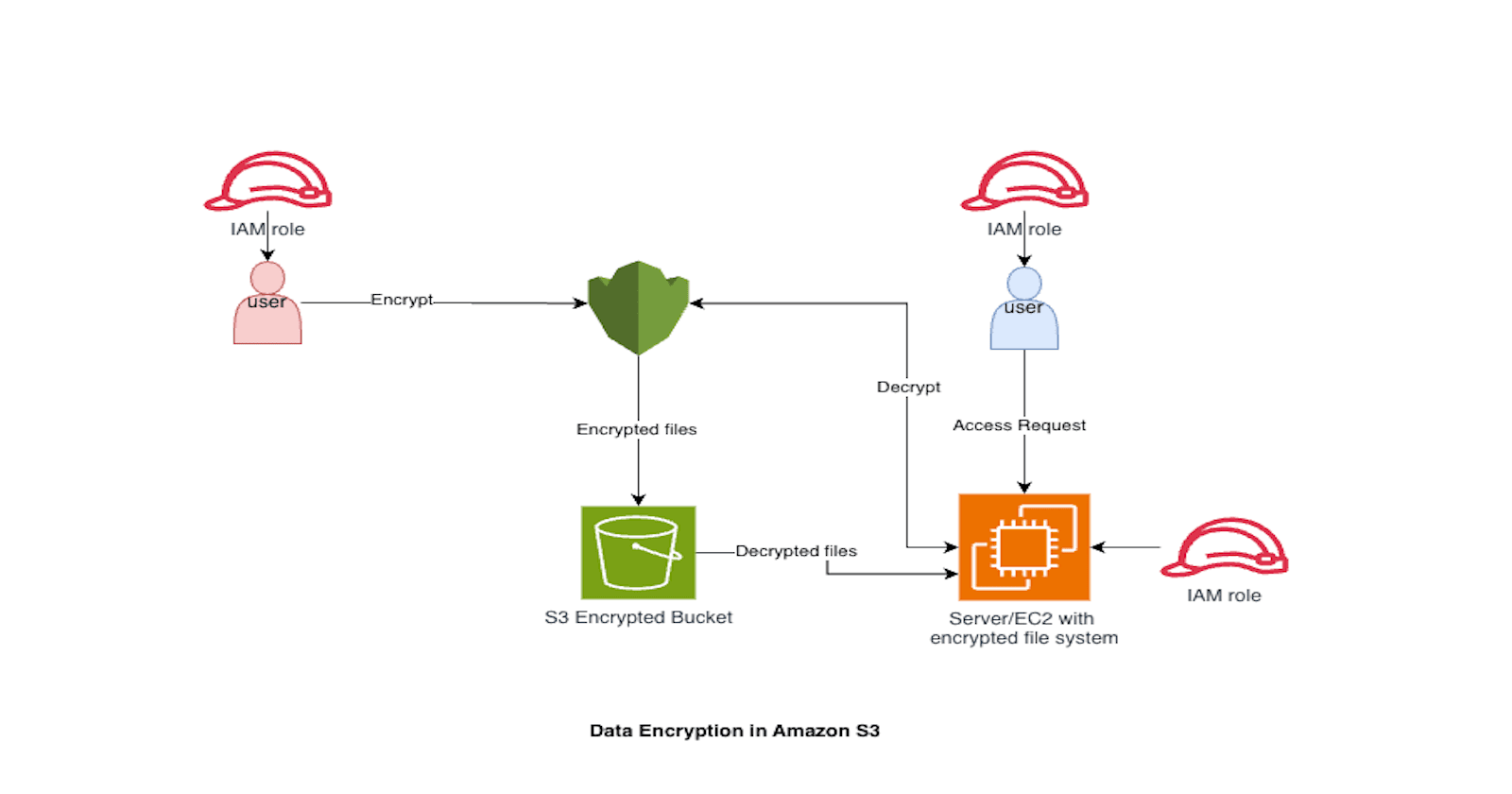
Data encryption is a critical component of cloud security, especially when dealing with sensitive workloads in regulated environments. Amazon S3 provides multiple encryption mechanisms that cater to different compliance and operational needs. This guide goes beyond the basics, diving into advanced configurations, key management strategies, and best practices for enterprise-grade security.
Why Encrypt Data in S3?
Encryption ensures that even if data is accessed without authorization, it remains unreadable. For enterprises, encryption is not optional—it’s a compliance mandate. AWS offers encryption at rest and in transit, but understanding the nuances of each method is key to building a secure architecture.
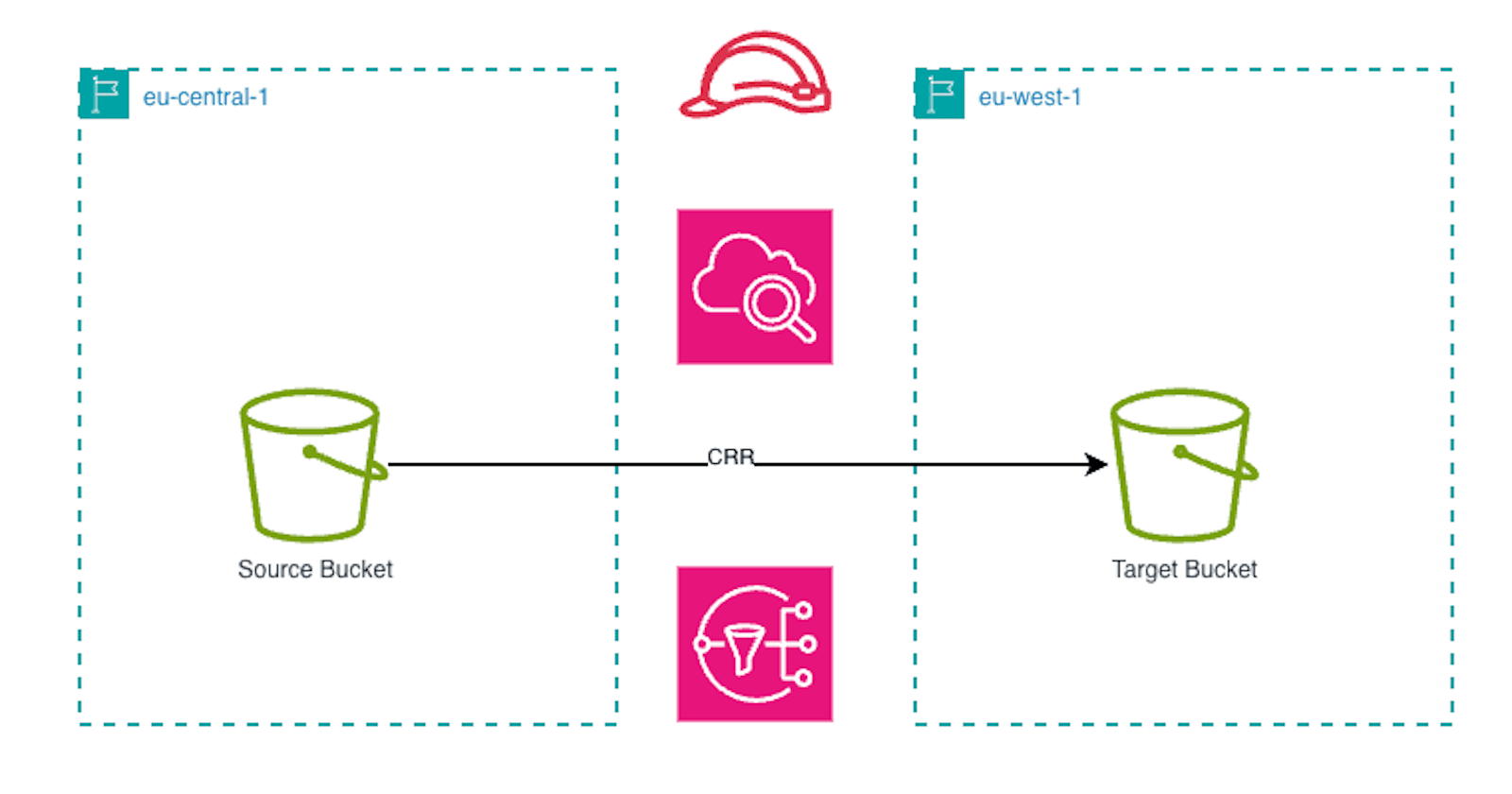
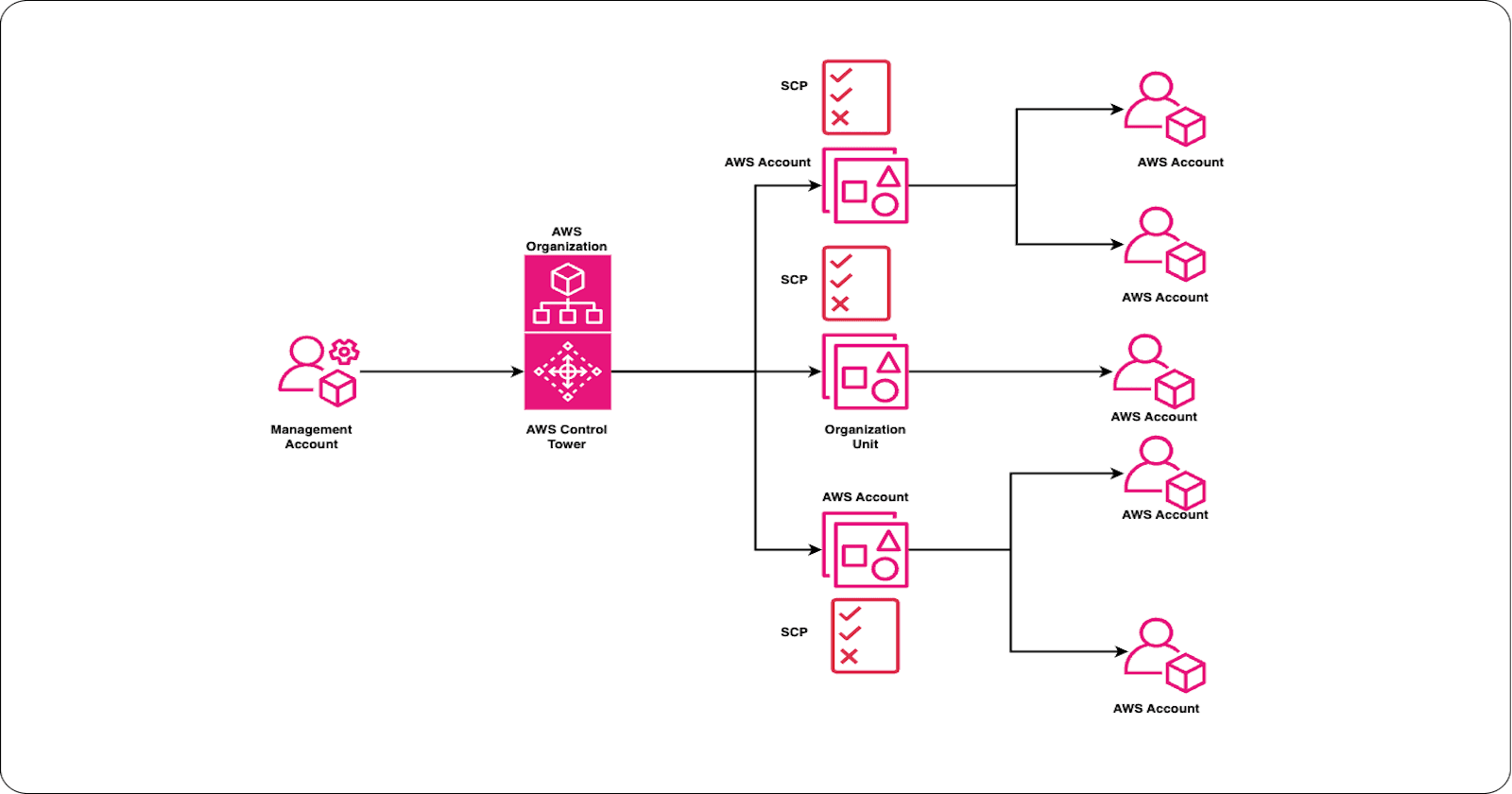
Advanced Consideration: Evaluate encryption requirements based on data classification, regulatory frameworks (e.g., GDPR, HIPAA), and internal security policies. For multi-account setups, enforce encryption through Service Control Policies (SCPs) and AWS Config rules.
Encryption Options in Amazon S3
AWS S3 supports two primary encryption paradigms: Server-Side Encryption (SSE) and Client-Side Encryption. Each has advanced features that can be leveraged for enterprise use cases.
1. Server-Side Encryption (SSE)
Server-side encryption with Amazon S3 is by far the simplest option and requires very little effort to enable. All you need to do is set the server-side encryption flag in the object metadata when uploading your data. Once your data reaches S3, it is encrypted automatically and stored securely. When you retrieve the data, Amazon S3 decrypts it seamlessly as it streams back to your application, so the process is completely transparent to you.
The key advantage of server-side encryption is that AWS manages the encryption keys on your behalf, making it incredibly easy to adopt without changing your application logic. Your data remains encrypted at rest in S3, and you don’t need to worry about key storage or rotation. This approach is ideal for organisations looking for a quick, compliant solution without the complexity of managing encryption keys themselves. AWS encrypts data before writing it to disk.
SSE-S3 (AES-256): Simplest option; AWS manages keys. Ideal for workloads where compliance does not require customer-managed keys.
SSE-KMS: Integrates with AWS Key Management Service for granular control, key rotation, and audit trails. Supports encryption context for additional security metadata.
SSE-C: Customer-provided keys; AWS never stores your key. Requires strict operational discipline for key lifecycle management.

Advanced Option: Use bucket policies to enforce SSE-KMS and deny uploads without encryption headers. Combine with KMS key policies for least privilege access.
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "DenyIncorrectEncryption",
"Effect": "Deny",
"Principal": "*",
"Action": "s3:PutObject",
"Resource": "arn:awsN:s3:::bucket-br/*",
"Condition": {
"StringNotEquals": {
"s3:x-amz-server-side-encryption": "aws:kms"
}
}
},
{
"Sid": "DenyNonKMSKey",
"Effect": "Deny",
"Principal": "*",
"Action": "s3:PutObject",
"Resource": "arn:awsN:s3:::bucket-br/*",
"Condition": {
"Null": {
"s3:x-amz-server-side-encryption-aws-kms-key-id": "true"
}
}
}
]
}
2. Client-Side Encryption
Client-side encryption is an alternative approach for securing your sensitive data before it ever leaves your environment/application. Unlike server-side encryption, this method ensures that your data remains encrypted throughout its journey, giving you complete control over the encryption keys. By using the AWS SDK for Java, you can implement client-side encryption with the AmazonS3EncryptionClient, which replaces the standard AmazonS3Client. The transition is straightforward because the encryption client shares the same interface as the standard client, meaning existing code requires minimal changes. Once configured, the client automatically encrypts data as it streams to Amazon S3 and decrypts it when retrieved, ensuring seamless integration with your application.
The key distinction between server-side and client-side encryption lies in key management. With client-side encryption, you are responsible for providing EncryptionMaterials, which dictate how the encryption process operates. This added responsibility offers stronger security because AWS never sees your unencrypted data or your keys. However, it also means you must implement robust key management practices, including secure storage, rotation, and access control, to maintain compliance and prevent vulnerabilities.
AWS SDKs: Provide built-in support for client-side encryption using envelope encryption.
Custom Implementations: Allows integration with on-prem HSMs or external key managers for hybrid architectures.
Advanced Option: For high-security environments, integrate client-side encryption with AWS Encryption SDK and implement data key caching for performance optimization.
How to Enable Encryption
a. SSE-S3
Enable default encryption in the bucket settings. AWS applies AES-256 automatically. Use S3 Object Lock with SSE-S3 for immutable storage in compliance scenarios.
b. SSE-KMS
Create a Customer Managed Key (CMK) in AWS KMS.
Configure IAM and bucket policies for controlled access.
Apply encryption during upload using CLI or SDK:
aws s3 cp file.txt s3://bucket-name/ --sse aws:kms --sse-kms-key-id <key-id>
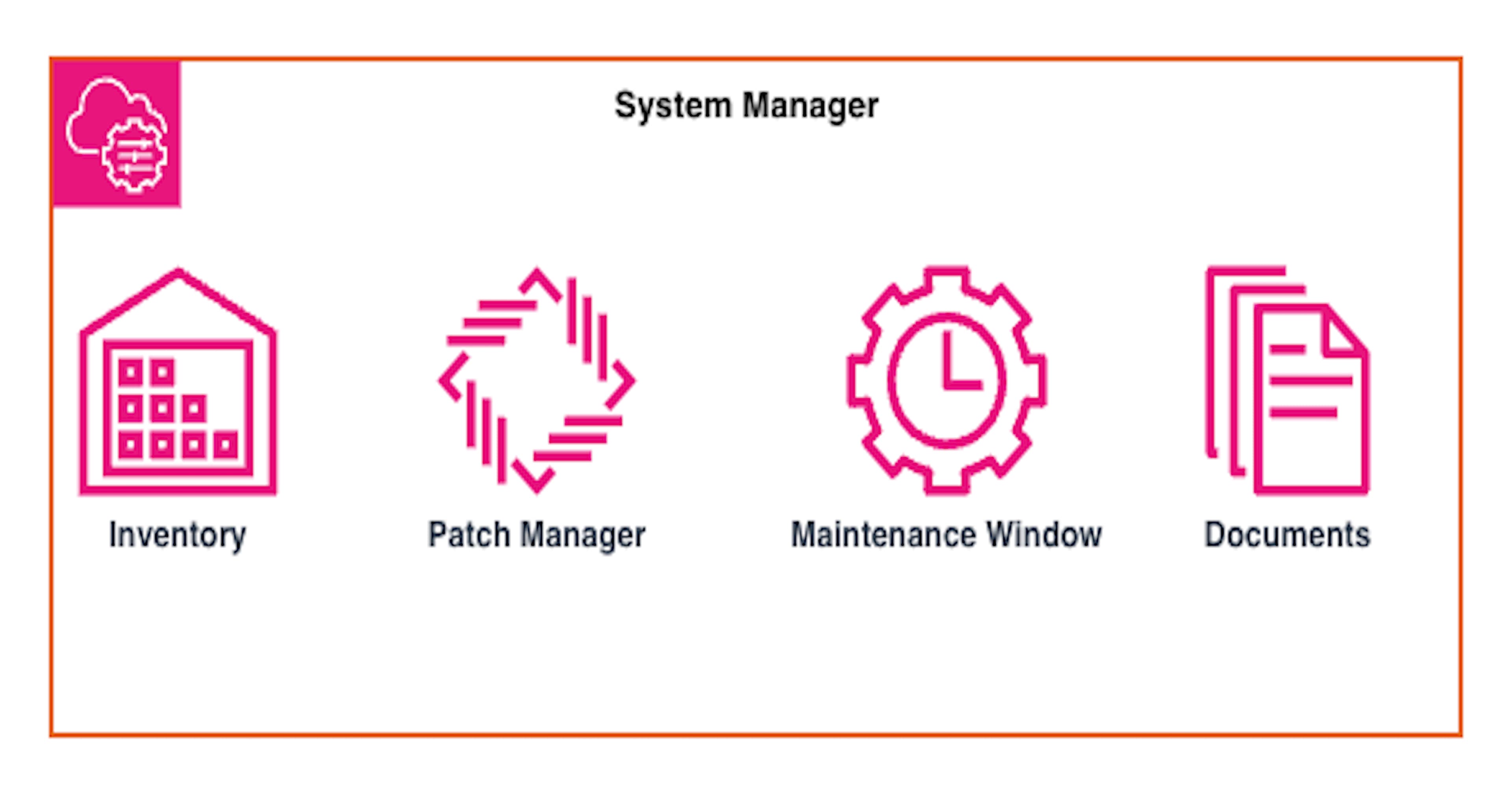
Enable automatic key rotation and monitor key usage with CloudTrail for compliance audits.
c. SSE-C
Provide your own key in the request header:
aws s3 cp file.txt s3://bucket-name/ --sse-c --sse-c-key <base64-encoded-key>
Implement a secure key distribution mechanism and audit access logs regularly.
Best Practices
Enforce encryption using bucket policies and AWS Config rules.
Use SSE-KMS for workloads requiring compliance and auditability.
Rotate keys periodically and enable multi-region keys for disaster recovery.
Monitor encryption compliance with AWS Security Hub and CloudTrail.
For hybrid environments, integrate with AWS PrivateLink for secure KMS access
Conclusion
Encryption in AWS S3 is more than a checkbox—it’s a strategic decision that impacts compliance, security posture, and operational complexity. By leveraging advanced features like SSE-KMS, encryption context, and client-side encryption, you can build a robust, enterprise-grade security model for your cloud workloads.